
Ricoh Printer Security Features
Enhance device, data and network security to help protect documents and other sensitive data from potential threats.

Wondering if your network printers are secure?
Cybersecurity threats are no longer limited to personal computers, servers or networks. Printing devices — even basic laser printers — need countermeasures against a diverse range of threats. As multifunction printers have evolved into true information terminals, they have become core IT assets in their own right.
The computing capability of printers and copiers has grown, but so too have potential threats. Secure print technology, commitment and know-how are essential. Ricoh can help you tackle potential printer security issues caused by vulnerabilities in your devices, the data they process and the networks to which they connect.
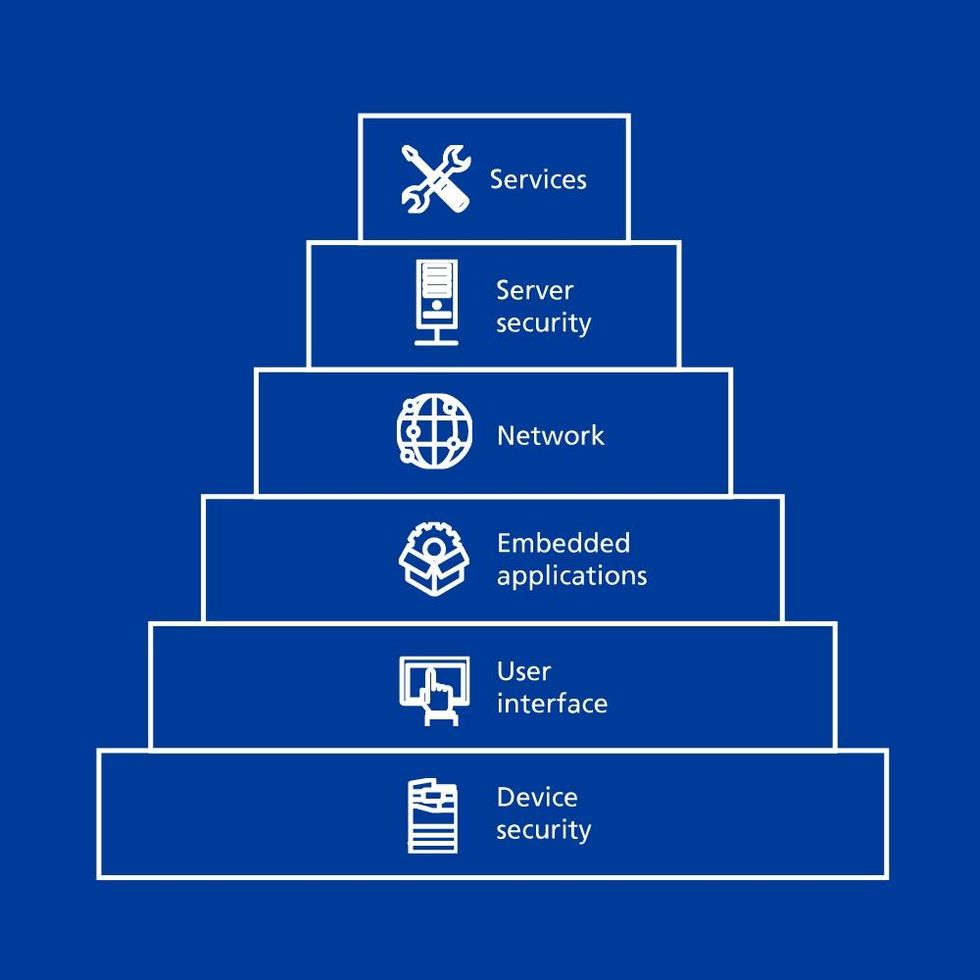
Ricoh’s layered approach to network printer security
At the heart of our printer security model is the device itself. The proprietary Ricoh operating system does not share vulnerabilities that are present in many operating systems, and many of our multifunction devices are certified to be IEEE 2600.2 as standard. Hard disk encryption and disk overwrite security ensure that processed data remains confidential.
Ricoh has worked hard to ensure that printer security is not weakened by the introduction of the Smart Operation Panel, which also uses a Ricoh-only OS. Unnecessary components are not installed, and root access is not available. Embedded applications must pass Ricoh compatibility testing and be digitally signed before they can run on the Smart Operation Panel. Ricoh’s commitment is to deliver products and services that comply with our customers’ IT and network security policies.

Data security is in our DNA
Ricoh printers and copiers are designed, manufactured and implemented with data security as a core requirement. Security-focused thinking is present from the start in everything from product design to sales. It’s in our DNA — informing both our design philosophy and our commitment to work continuously to support our customers with solutions as threats evolve.
Choose optional security features with our multifunction printer lineup
Help protect data and documents when printing, copying, scanning and faxing with Ricoh multifunction printers.
Security for Ricoh Multifunction Printers
Security Threats and Countermeasures
As a forerunner in the field of security countermeasures of multifunction printers, Ricoh addresses every conceivable security threat
Ricoh's Security Functions
An extensive range of security features can enable you to monitor, optimize and effectively manage document and information security.
Ricoh Products Certified with Common Criteria
To ensure that our devices have been designed and implemented in conformance with specific security standards, many Ricoh products are indepently tested and verified.




